Hybrid Chaotic-DNA Cryptosystem With Galois Field Diffusion For Secure Color Image Encryption
DOI:
https://doi.org/10.5281/zenodo.19977269Keywords:
Chaotic Maps, DNA Cryptography, Color Image Encryption, Galois Field, Pixel Scrambling, Information Entropy, Image SecurityAbstract
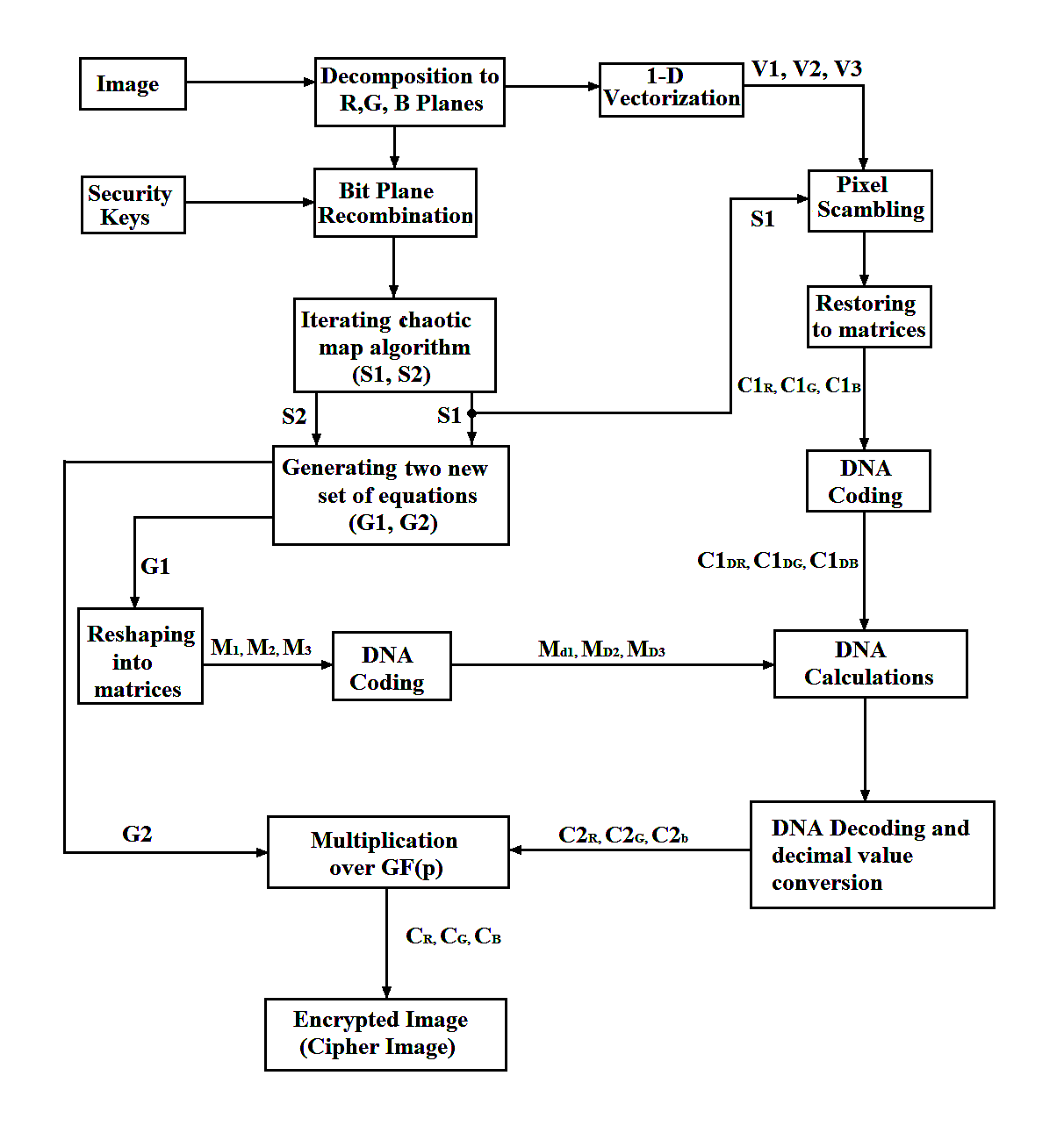
Security issues in digital image transmission have become an important concern in multimedia communication. Because of their large image data volume, high redundancy and strong correlation among the neighboring pixels, the conventional encryption algorithms are not suitable for practical image encryption. In this paper, a chaotic color image encryption scheme based on Deoxyribonucleic Acid (DNA) coding calculation, multiplication arithmetic over the Galois field GF(17) and improved one-dimensional (1D) chaotic maps is presented. To address the limitations of classical 1D maps, including a narrow chaotic range and non-uniformity, three modified 1D chaotic maps, namely, Sine-Logistic Map (SLM), Chebyshev-Logistic Map (CLM) and Sine-Chebyshev Map (SCM) have been proposed. Furthermore, the chaotic initial values are modified using the plain image (the input color image is decomposed into Red, Green and Blue (R, G and B) planes, and bit-plane recombination is carried out), which makes it possible to defend against chosen-plaintext and known-plaintext attacks. In this scheme, the image pixels are first scrambled using chaotic sequences, and then DNA coding is applied. After DNA coding, DNA arithmetic operations are performed, and then DNA decoding is applied. In order to further diffuse the pixels, multiplication over GF(17) is applied. Security analysis, including histogram uniformity, information entropy, and inter-pixel correlation coefficients, demonstrates that the proposed scheme is secure.
References
[1] Y. Wu, J. P. Noonan, G. Yang, and H. Jin, "Image encryption using the two-dimensional logistic chaotic map," J. Electron. Imag., vol. 21, no. 1, p. 013014, 2012.
[2] Z. Hua, Y. Zhou, C.-M. Pun, and C. L. P. Chen, "2D Sine Logistic modulation map for image encryption," Inf. Sci., vol. 297, pp. 80–94, Mar. 2015.
[3] C. Fu, G.-Y. Zhang, M. Zhu, Z. Chen, and W.-M. Lei, "A new chaos-based color image encryption scheme with an efficient substitution keystream generation strategy," Secur. Commun. Netw., vol. 2018, p. 2708532, 2018.
[4] X. Chai, Y. Chen, and L. Broyde, "A novel chaos-based image encryption algorithm using DNA sequence operations," Opt. Lasers Eng., vol. 88, pp. 197–213, Jan. 2017.
[5] L. Huang, S. Wang, J. Xiang, and Y. Sun, "Chaotic color image encryption scheme using DNA coding calculations and arithmetic over the Galois field," Math. Probl. Eng., vol. 2020, p. 3965281, 2020.
[6] J. Fridrich, "Symmetric ciphers based on two-dimensional chaotic maps," Int. J. Bifurc. Chaos, vol. 8, no. 6, pp. 1259–1284, 1998.
[7] S. Bahri-Laleh, M. A. Balafar, and M.-R. Feizi-Derakhshi, "A stream cipher method for RGB image encryption using PSO base key generation," Int. J. Secur. Its Appl., vol. 11, no. 9, pp. 73–94, 2017.
[8] C. Fu et al., "A new chaos-based color image encryption scheme," Secur. Commun. Netw., 2018.
[9] Z. Hua et al., "2D Sine Logistic modulation map," Inf. Sci., 2015.
[10] W. Stallings, Cryptography and Network Security, 4th ed. Pearson Education India, 2006.
[11] H. Liu, X. Wang et al., "Image encryption using DNA complementary rule and chaotic maps," Appl. Soft Comput., vol. 12, no. 5, pp. 1457–1466, 2012.
[12] R. Zhang et al., "A novel plaintext-related color image encryption scheme based on cellular neural network and Chen's chaotic system," Symmetry, vol. 13, no. 3, p. 393, 2021.
[13] Y. Liu and J. Zhang, "A multidimensional chaotic image encryption algorithm based on DNA coding," Multimed. Tools Appl., vol. 79, pp. 21579–21601, 2020.
[14] X. Yan, X. Wang, and Y. Xian, "Chaotic image encryption algorithm based on arithmetic sequence scrambling model and DNA encoding operation," Multimed. Tools Appl., vol. 80, pp. 10949–10983, 2021.
[15] Q. Li and L. Chen, "An image encryption algorithm based on 6-dimensional hyper chaotic system and DNA encoding," Multimed. Tools Appl., vol. 83, pp. 5351–5368, 2024.
[16] Q. Wang, X. Zhang, and X. Zhao, "Color image encryption algorithm based on bidirectional spiral transformation and DNA coding," Phys. Scr., vol. 98, p. 025211, 2023.
[17] L. M. Adleman, "Molecular computation of solutions to combinatorial problems," Science, vol. 266, no. 5187, pp. 1021–1024, 1994.
[18] M. Babaei, "A novel text and image encryption method based on chaos theory and DNA computing," Nat. Comput., vol. 12, no. 1, pp. 101–107, 2013.
[19] S. Al-Maadeed, A. Al-Ali, and T. Abdalla, "A new chaos-based image-encryption and compression algorithm," J. Electr. Comput. Eng., vol. 2012, p. 179693, 2012.
Downloads
Published
Data Availability Statement
The benchmark images employed in this study are freely accessible from the USC-SIPI Image Database (https://sipi.usc.edu/database/). The Python implementation code is available from the corresponding author upon reasonable request.
Issue
Section
License
Copyright (c) 2026 International Journal of Computational Intelligence in Engineering (IJCIE)

This work is licensed under a Creative Commons Attribution-ShareAlike 4.0 International License.